TLS automation configuration script for Artemis System Service
-
Run Certs Installer Script. in
./kubernetes/scriptschmod +x generate-artemis-certs.sh ./generate-artemis-certs.sh -
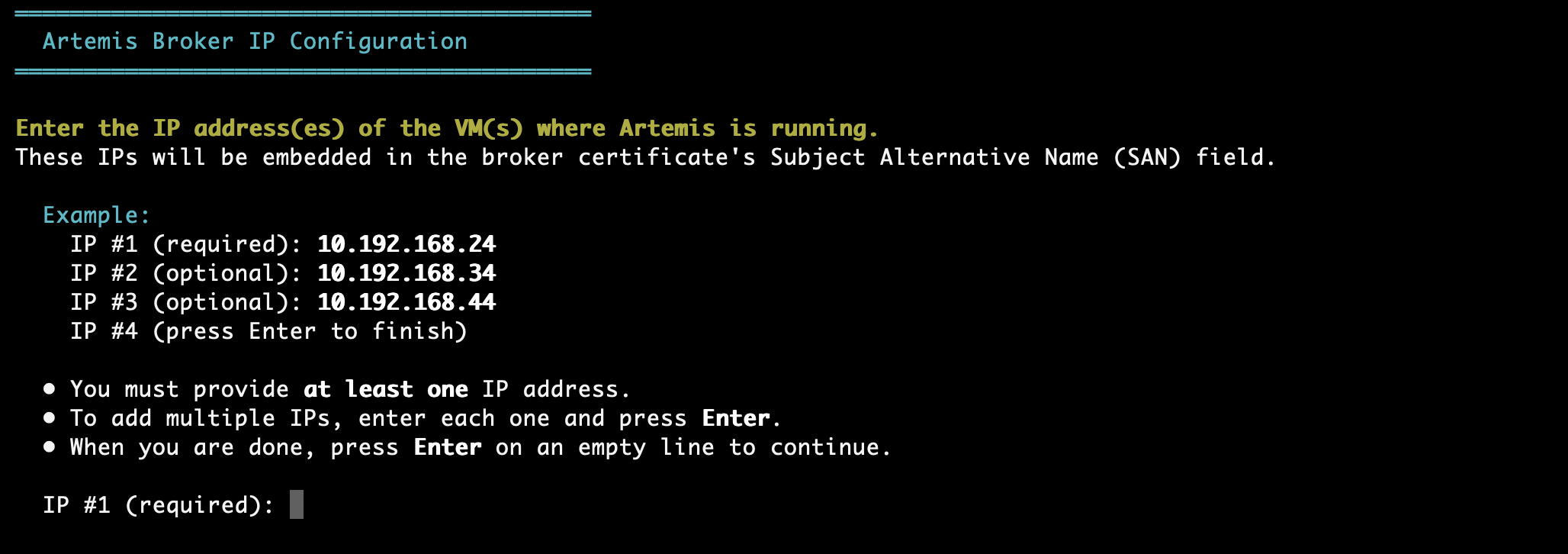
You will be prompted to add at least 1 IP(s) to generate your certificate files. Provide IP(s) where your pods and Artemis is running.
-
Recreate the AMQ-TLS secret while in
./kubernetes### Delete AMQ TLS Secret kubectl delete secret activemq-tls -n expertflow ### Apply AMQ TLS Secret kubectl apply -f pre-deployment/static-tls/activemq-tls.yaml -
When deploying CX Core, update these variables in
helm-values/ef-cx-custom-values.yaml# helm-values/ef-cx-custom-values.yaml efConnectionVars: ACTIVEMQ_SSL_VERIFY_HOST: "true" ACTIVEMQ_SSL_TRUST_ALL: "false" -
Restart pods if there are any pods running, to be able to establish a connection with newly generated certificates.
### Restart pods in expertflow namespace k delete pods -n expertflow --all