Requirements
- Kubernetes. Deployment Planning
- Storage Solution Storage Solution - Getting Started
- CX Deployement Helm-based Deployment for Expertflow CX
Pre-Requisite if QM-connector is enabled
-
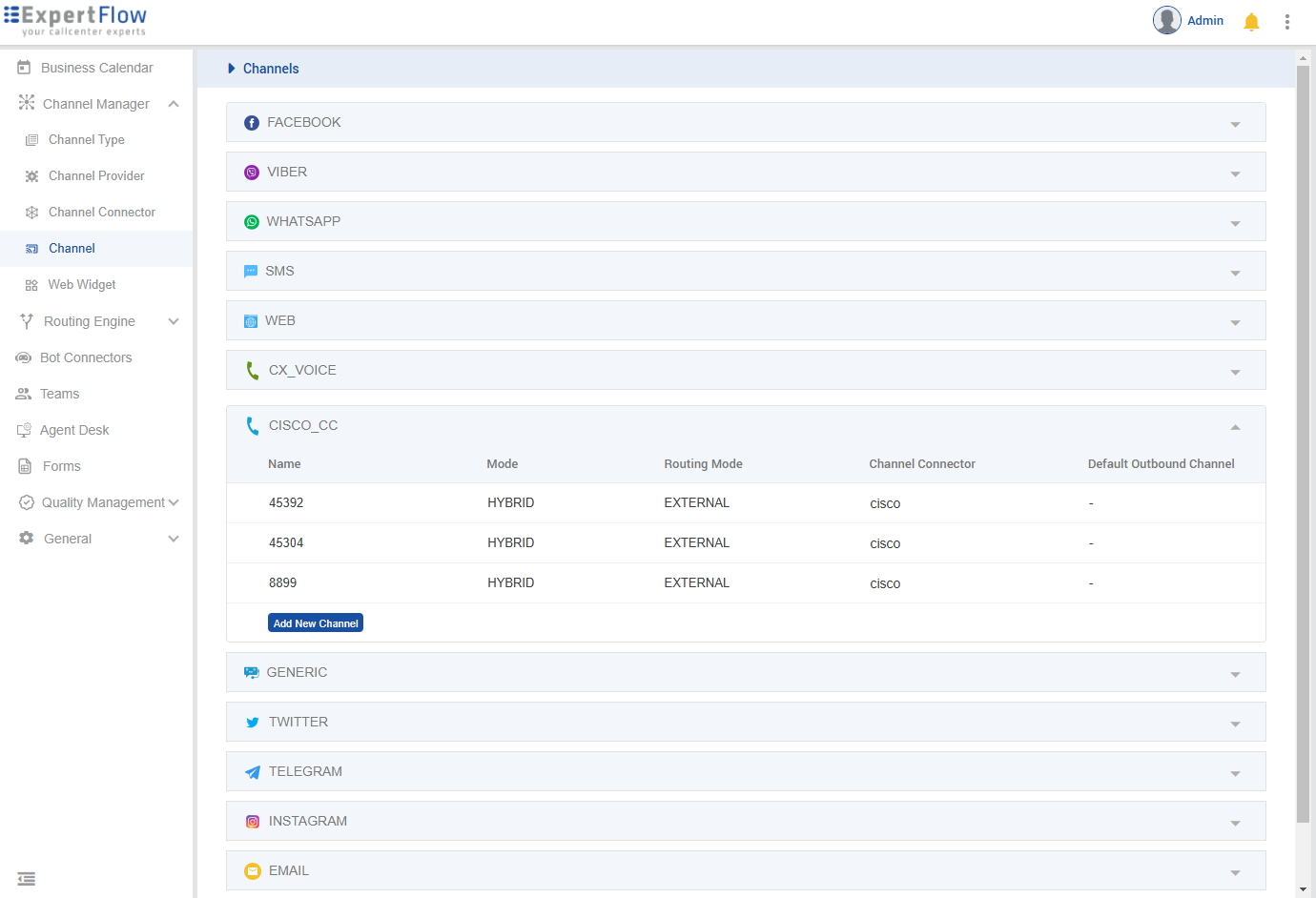
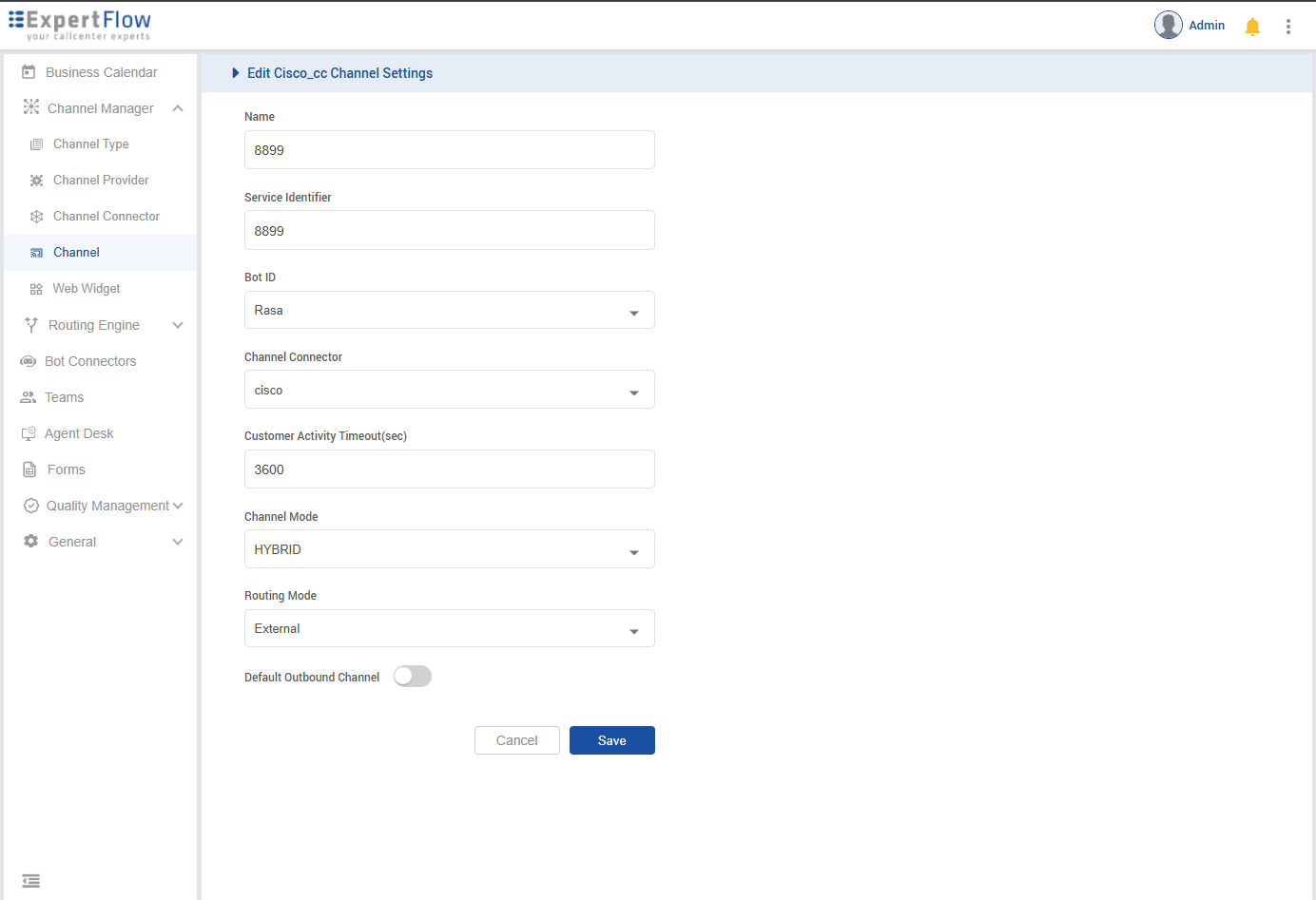
Create New Channels of CISCO_CC for both Inbound and Outbound, for outbound select a 4-5 Digit Number, and set it as
UCCE_OB_SERVICE_IDENTIFIERinvalues.yaml
-
Set Routing Mode as External
-
Set the Channel Model as HYBRID
-
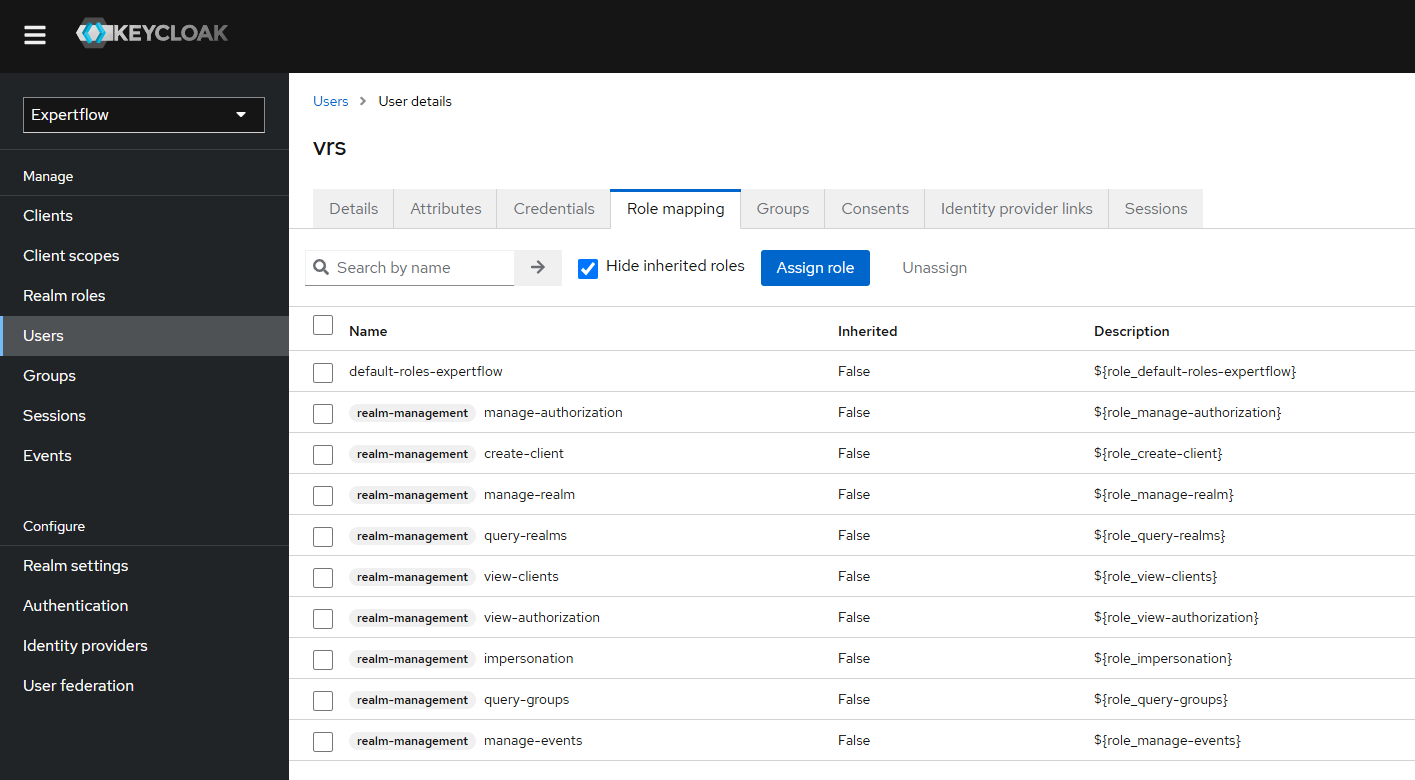
Create a new user in Realm, set its name & password as ‘vrs’, and assign all the ‘realm-management’ roles to that user. Set
KEYCLOAK_USERNAME & KEYCLOAK_PASSWORDinvalues.yaml
Deployment
Add the Expertflow Helm charts repository.
helm repo add expertflow https://expertflow.github.io/charts
Update the charts repository
helm repo update expertflow
Clone QM Repository
git clone -b CX-4.8 https://efcx:RecRpsuH34yqp56YRFUb@gitlab.expertflow.com/cim/cim-solution.git CX-4.8
cd CX-4.8/kubernetes
Create a database with name qm_backend in Postgres.
export the admin username/password pair for postgresql-client pod
export POSTGRES_ADMIN_PASSWORD=$(kubectl get secret --namespace ef-external ef-postgresql -o jsonpath="{.data.postgres-password}" | base64 -d)
and for sa user ( default user for EF-CX component using PostgreSQL database )
export POSTGRES_PASSWORD=$(kubectl get secret --namespace ef-external ef-postgresql -o jsonpath="{.data.password}" | base64 -d)
launch the postgresql client
kubectl run ef-postgresql-client --namespace ef-external --image docker.io/bitnami/postgresql:14.5.0-debian-11-r21 --env="PGPASSWORD=$POSTGRES_PASSWORD" --command -- sleep infinity
once the pod is running, exec into the postgresql-client pod
kubectl -n ef-external exec -it ef-postgresql-client -- bash
execute the environment setup for postgresql-client ( Only needed when the postgresql is running in non-HA mode , like no pgpool and multiple replicas of postgresql are running )
/opt/bitnami/scripts/postgresql/entrypoint.sh /bin/bash
Log into Postgres using the following command:-
psql --host ef-postgresql -U sa postgres -p 5432
Create db and extensions using the following commands:-
CREATE DATABASE qm_db;
\c qm_db;
CREATE EXTENSION IF NOT EXISTS "uuid-ossp";
Then to exit from the shell
\q
exit
exit
Customise the deployment by fetching the helm chart’s values file and edit it as per requirements.
helm show values expertflow/qm --version 4.8.0 > helm-values/cx-qm-custom-values.yaml
Open the file cx-qm-custom-values.yaml and edit it according to the below given information, which is necessary for the qm-backend to work properly.
|
Value |
Updated Value |
|---|---|
|
ingressRouter |
FQDN of the host |
|
enabled (under qm-connector) |
To enable or disable qm-connector |
Update the following environment variables under QM-Connector
|
Env var |
Description |
Example values |
|---|---|---|
|
RECORDING_SERVER_FQDN |
Recording Server IP |
|
|
EFCX_FQDN |
CX FQDN |
|
|
CALL_BACK_URL |
Webhook for conversation creation |
|
|
UCCE_ENGINE |
UCCE DB Engine |
sqlserver |
|
UCCE_IP |
UCCE IP |
192.168.1.72 |
|
UCCE_PORT |
UCCE DB port |
1433 |
|
UCCE_DATABASE |
UCCE |
uc126_awdb |
|
UCCE_USERNAME |
UCCE |
sa |
|
UCCE_PASSWORD |
UCCE |
Expertfllow464 |
|
UCCE_OB_SERVICE_IDENTIFIER |
Service Identifier for outbound calls |
8899 |
|
KEYCLOAK_REALM_NAME |
Realm name from EFCX keycloak |
expertflow |
|
KEYCLOAK_CLIENT_ID |
KeyCloak client ID from EFCX keycloak |
cim |
|
KEYCLOAK_CLIENT_SECRET |
Add the client secret from the EFCX keycloak |
ef61df80-061c-4c29-b9ac-387e6bf67052 |
|
KEYCLOAK_USERNAME |
Keycloak User with all the realm-management Roles |
vrs |
|
KEYCLOAK_PASSWORD |
The password of the keycloak User with all the realm-management Roles |
vrs |
|
KEYCLOAK_AGENT_ROLE_NAME |
The role that needs to be assigned to the new Agent created with QM-connector |
agent |
|
KEYCLOAK_AGENT_ROLE_ID |
Role-Id that needs to be assigned to new Agent created with QM-connector |
1903735d-5bcc-4253-a05e-ea1487195c9c |
|
DB_NAME |
Name of the VRS database |
vrs |
|
DB_USER |
Username for VRS database |
sa |
|
DB_PASSWORD |
Password for the VRS database |
Expertflow123 |
|
DB_ENGINE |
The engine on which VRS database is running i.e MySQL |
sqlserver |
|
DB_HOST |
Name or IP of the host on which the VRS database is active |
192.168.1.126 |
|
DB_PORT |
Port of the VRS Database |
1433 |
|
DB_DRIVER |
Driver on which VRS database is running i.e mysql drive |
com.microsoft.sqlserver.jdbc.SQLServerDriver |
Finally, deploy the QM using the following command:-
helm upgrade --install --namespace=expertflow --set global.efCxReleaseName="ef-cx" qm --debug --values helm-values/cx-qm-custom-values.yaml expertflow/qm --version 4.8.0
Keycloak Configuration:
Quality Management has introduced two new roles:
-
Quality Manager
-
Evaluator
Following are the quality-manager-realm and quality-manager-authz files. First partial import realm to get the relevant Quality Management roles then import the permissions file to get all the quality-management related permissions.
4.7-quality-management-realm.json 4.7-quality-management-authz.json
Step by step process:
Step 1: Login to Keycloak
Access the Keycloak Administration console by opening this URL in your browser: https://<FQDN>/auth. and click on Administration Console.
Default username and password is “admin” and “admin” respectively.
Step 2: Open the Realm settings tab
In the ExpertFlow realm, select Realm Settings from the left navigation bar, then click on the Actions on top left. A pop up will open.
If the ExpertFlow realm is not present. Refer to this documentation to import the ExpertFlow realm and additional configuration
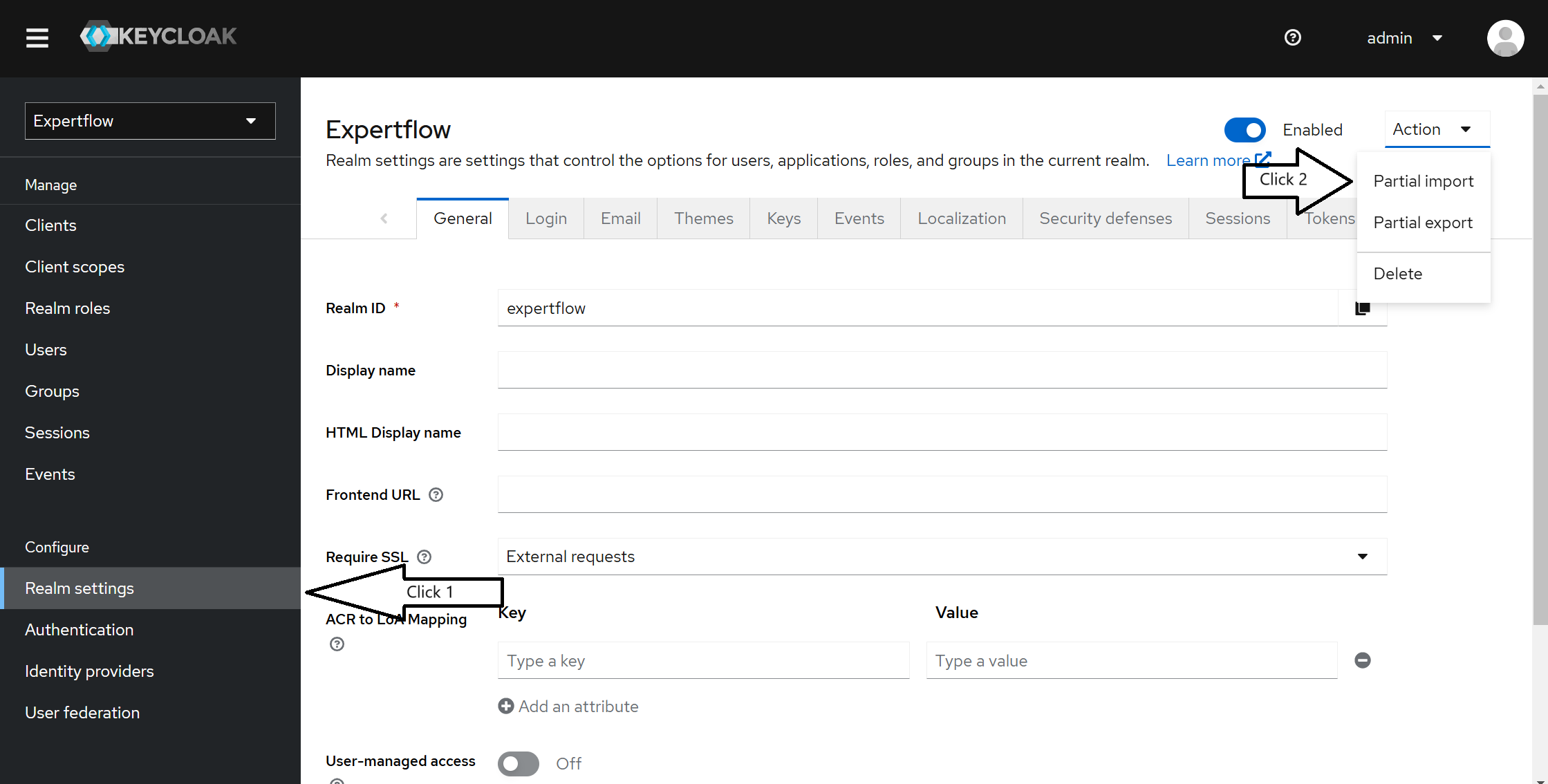
Step 3: Import the file with following settings:
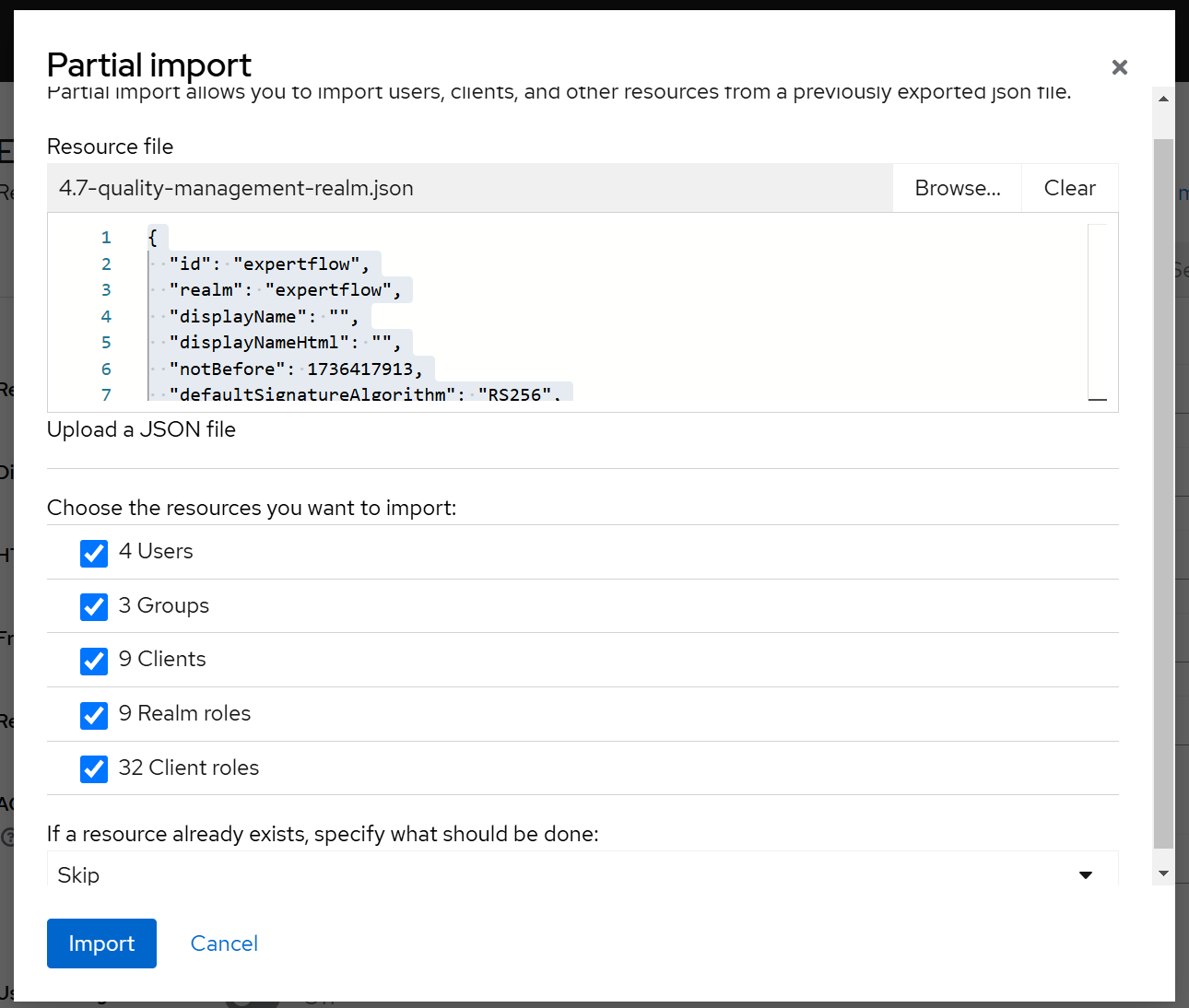
Choose all the resources and select skip for last dropdown in case of resource already exists. And click import. A successful import message will appear.
Step 4: Now go to Clients on side navigation bar and click on cim from client list.
Now click on Authorization tab like following and click on import.
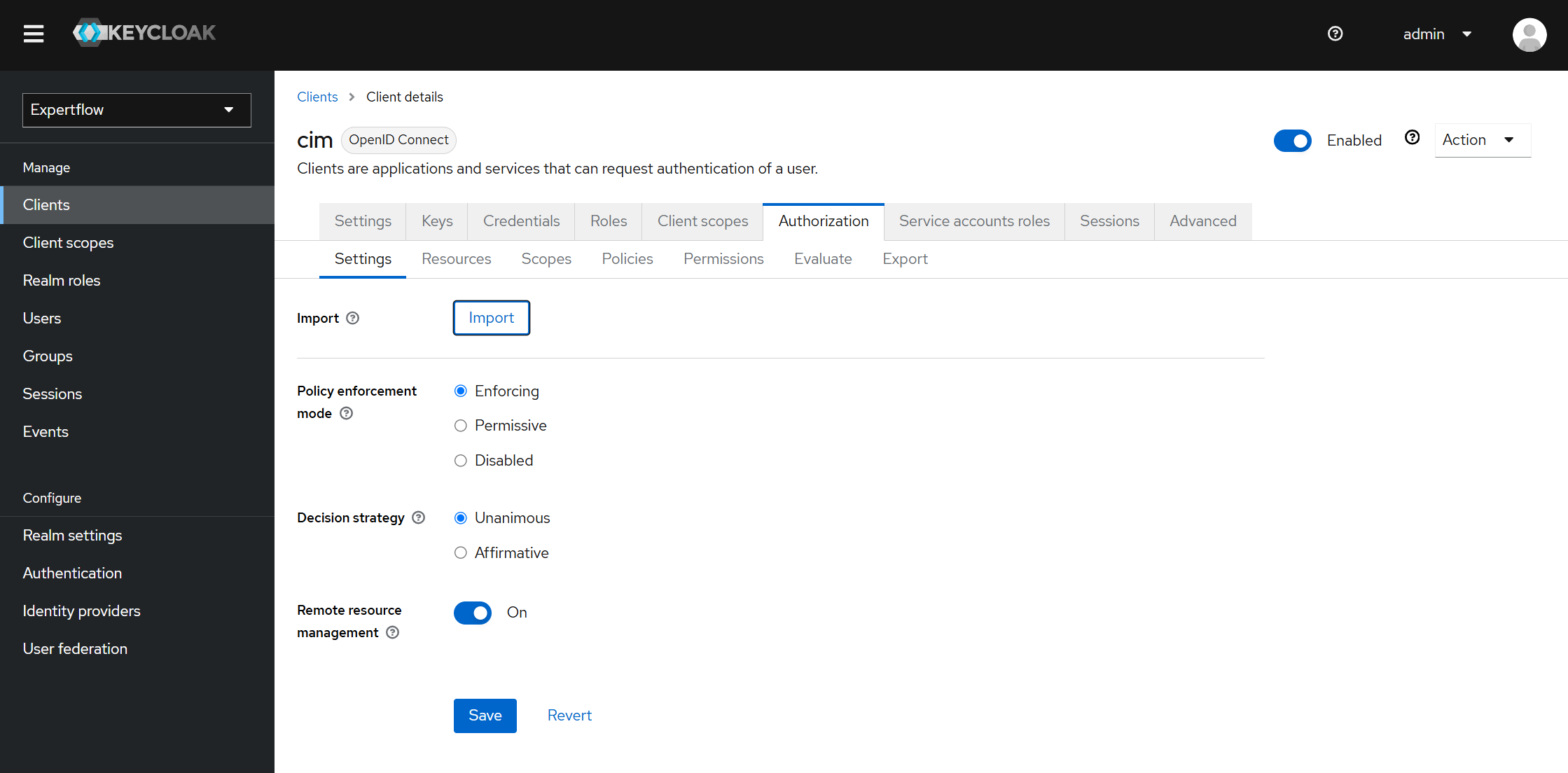
Step 5: Import the Auth file here using browse and click on Confirm.
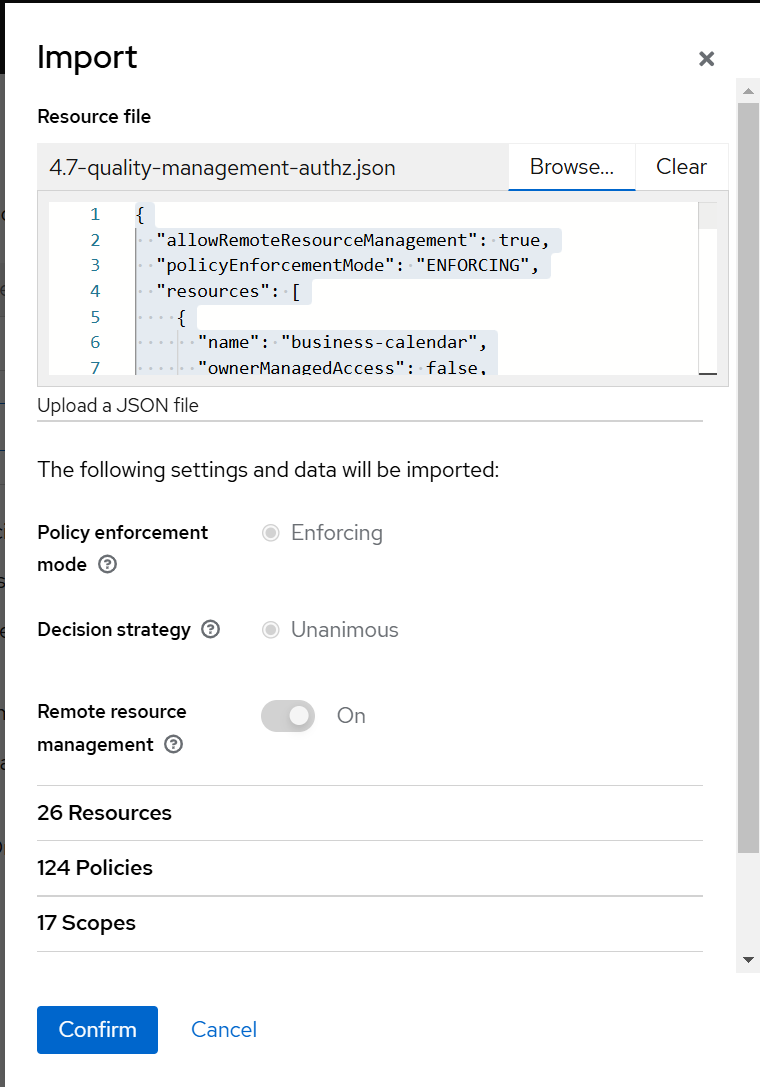
Now, all is done for importing realms and roles/permissions in Keycloak for Quality Management. In next section, you will see how to create users in keycloak and assign Quality Manager and Evaluator roles to them with groups.
Assigning role and group to user in Keycloak:
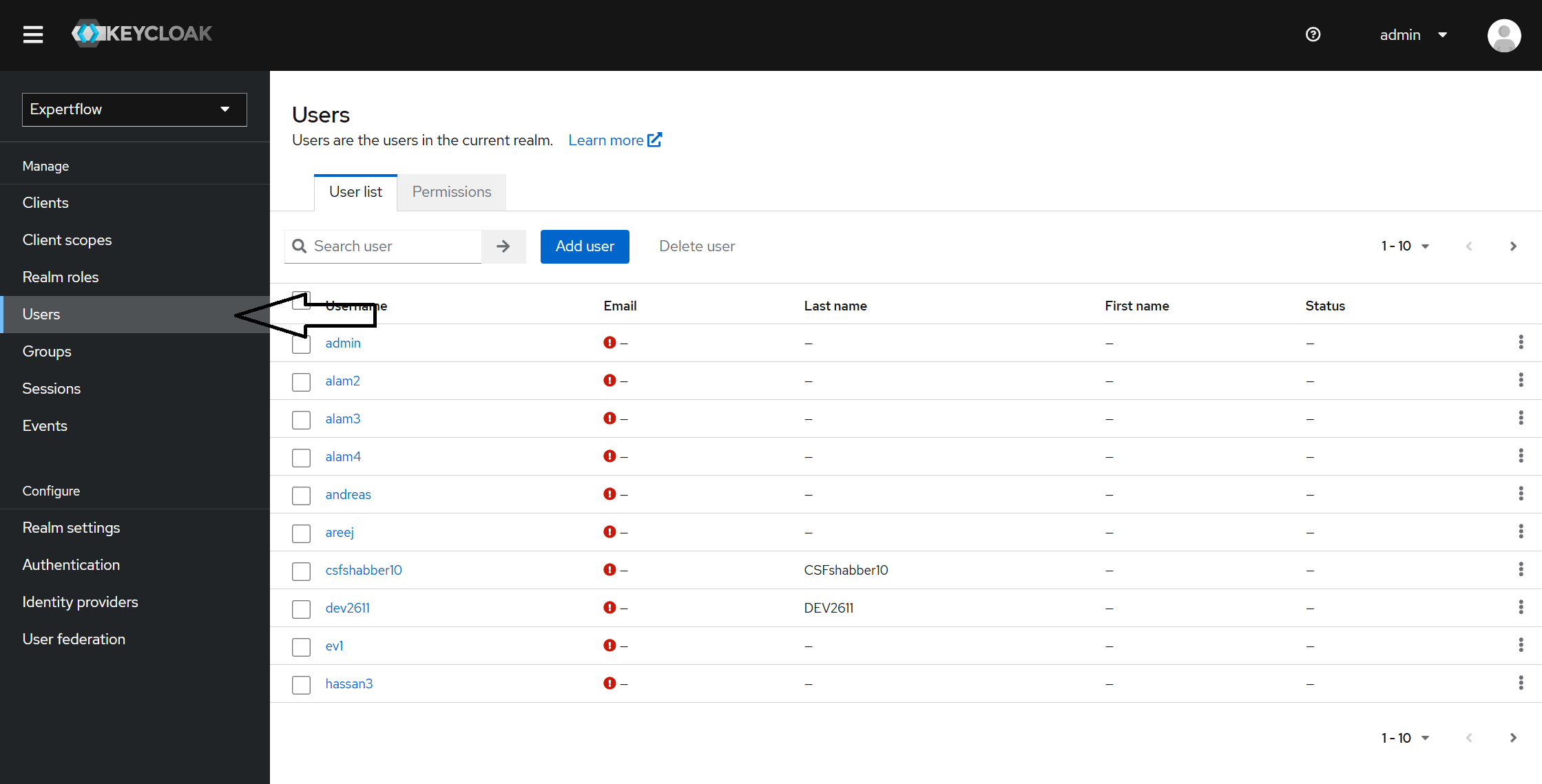
Step 1: Create a user in keycloak
Click on users on left sidebar navigation and click on Add user.
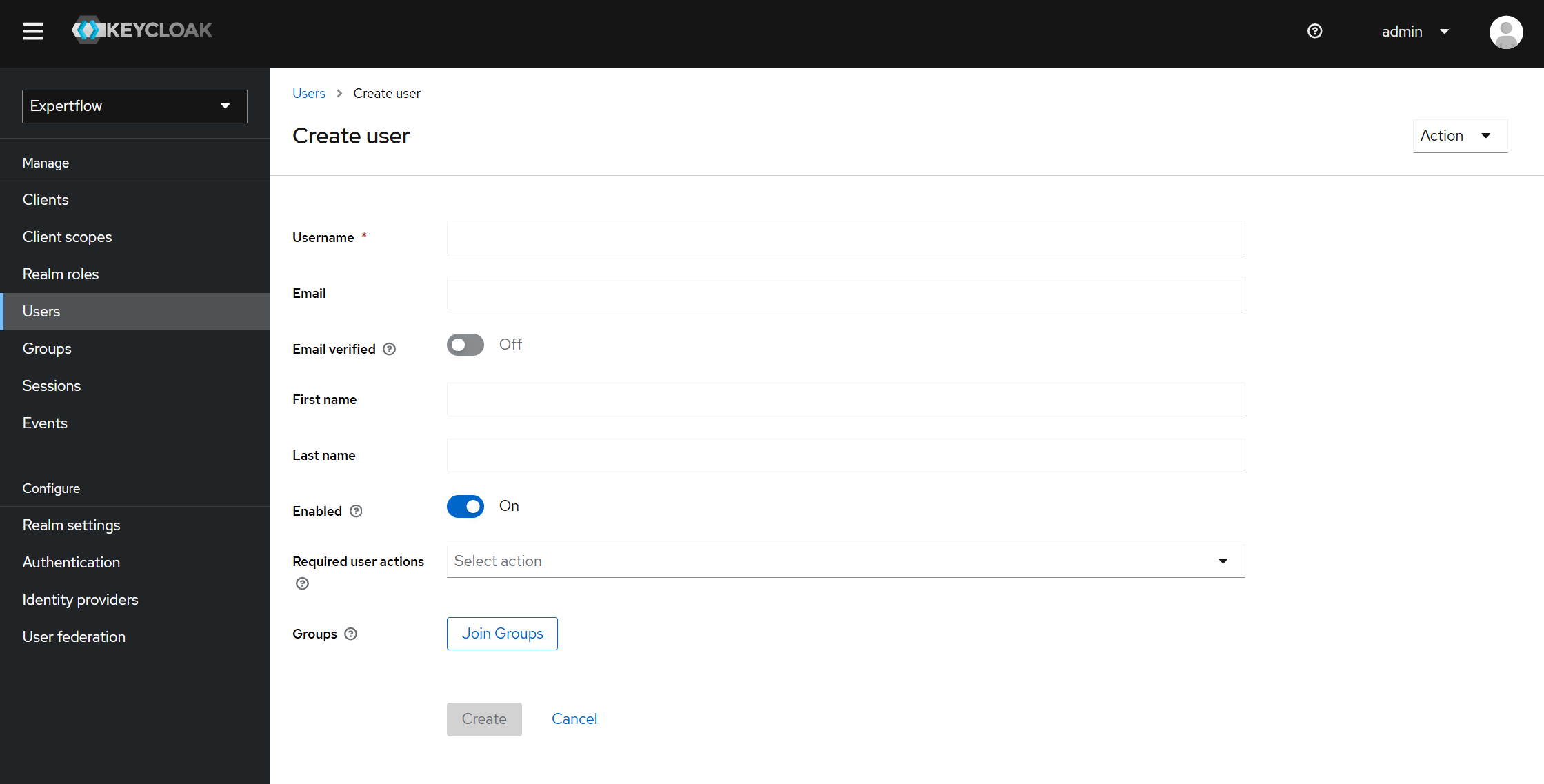
Step 2: Fill the following form:
Fill the form. Username is compulsory here and click on Create button below.
Step 3: Setting the Password
After creating the user, you will be taken to next screen. Click on Credentials tab, you will meet following screen.
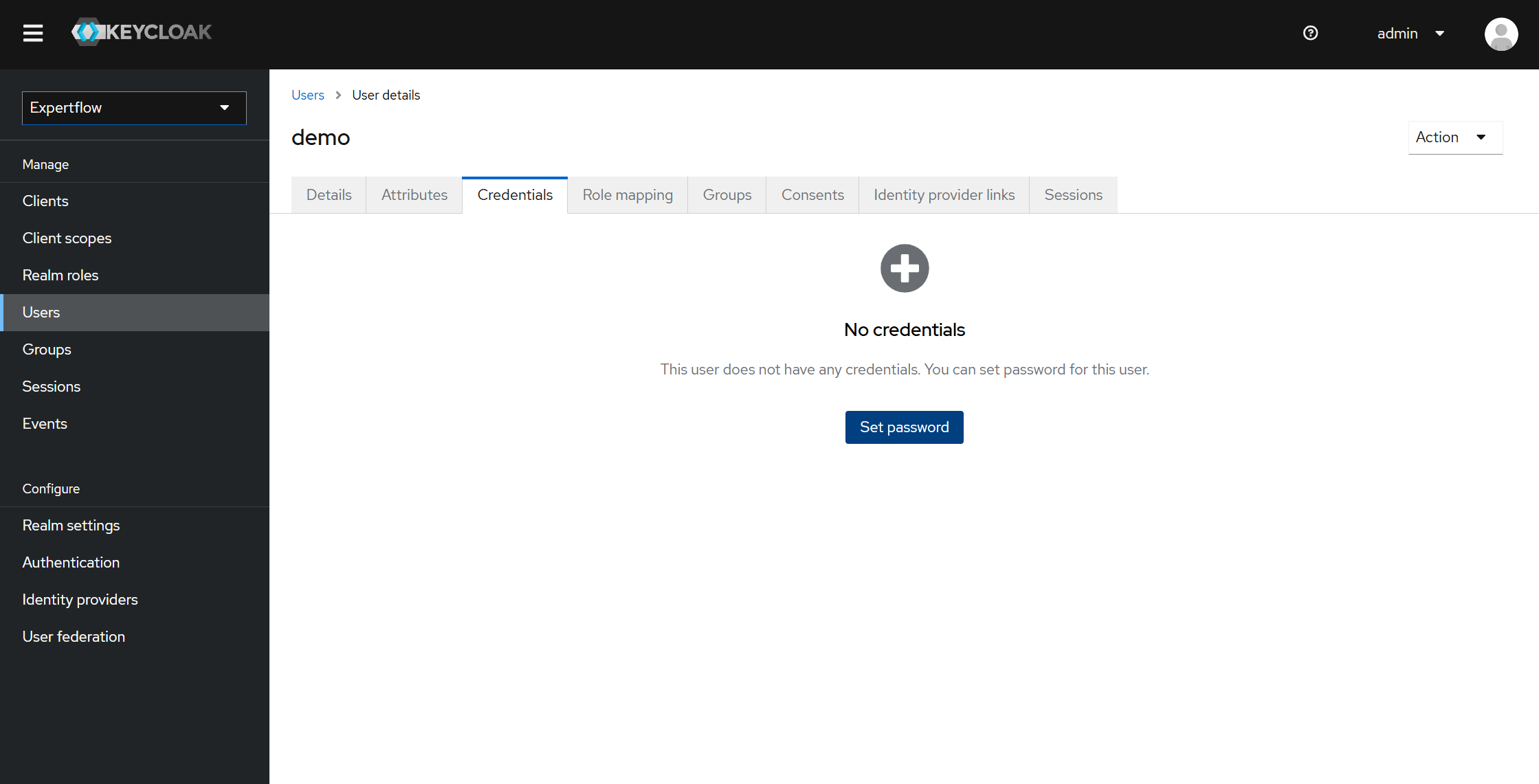
Click on Set Password. You will see following popup.
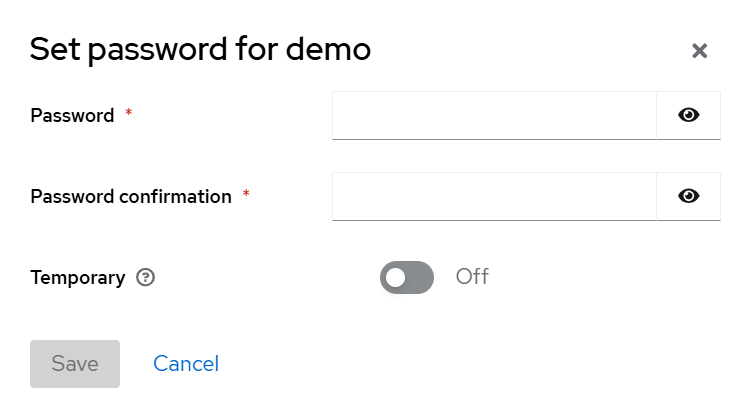
Fill out the password and confirm password fields and make sure to toggle off Temporary otherwise you user will be deleted after certain time as it will be temporary user. After that click and Save. You will again asked for confirmation, click on Save Password.
Step 4: Assigning Roles to user:
Click on Role Mapping tab. You will see following screen. Click on Assign Role button in blue color.
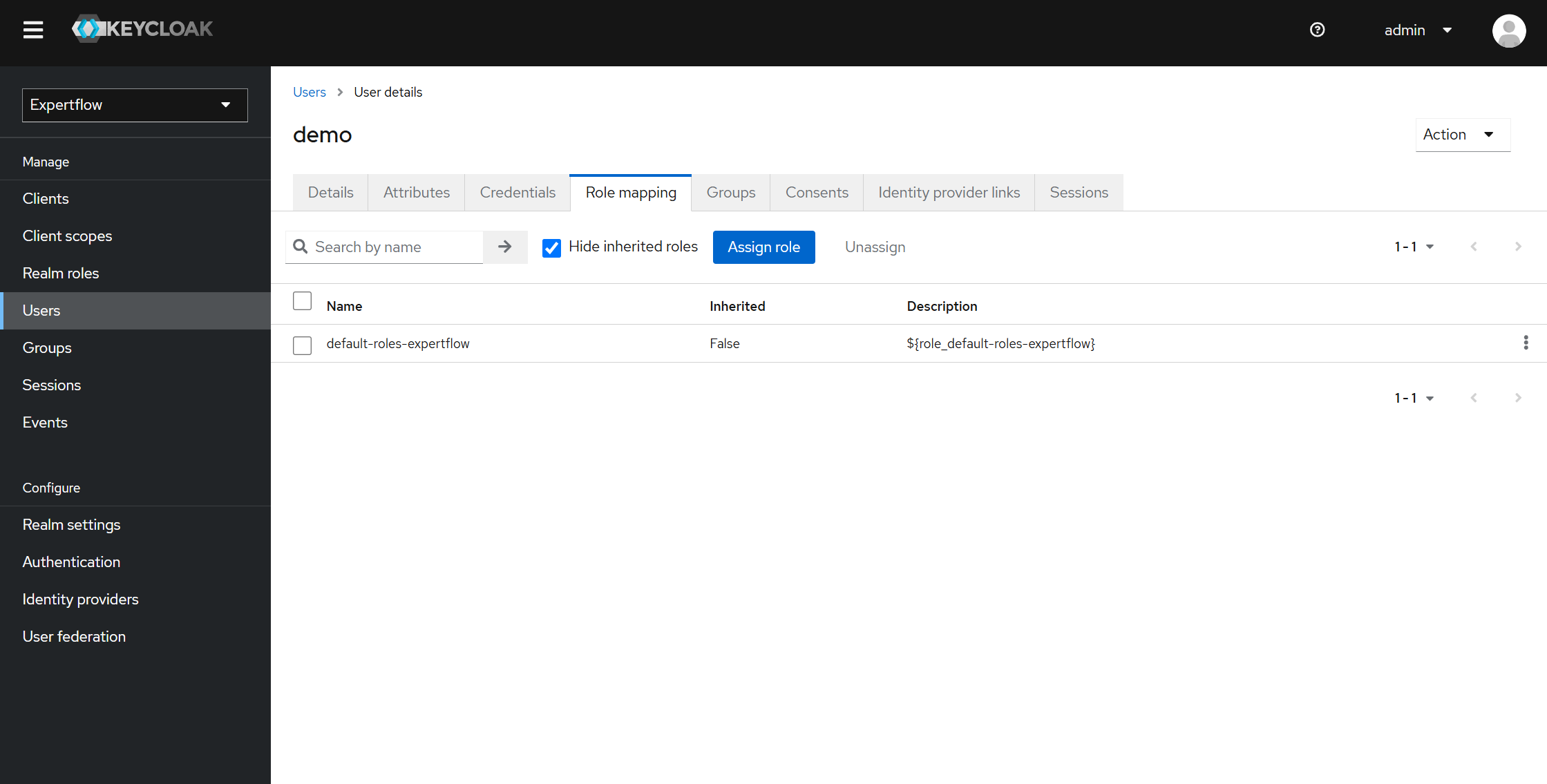
You will meet following screen.
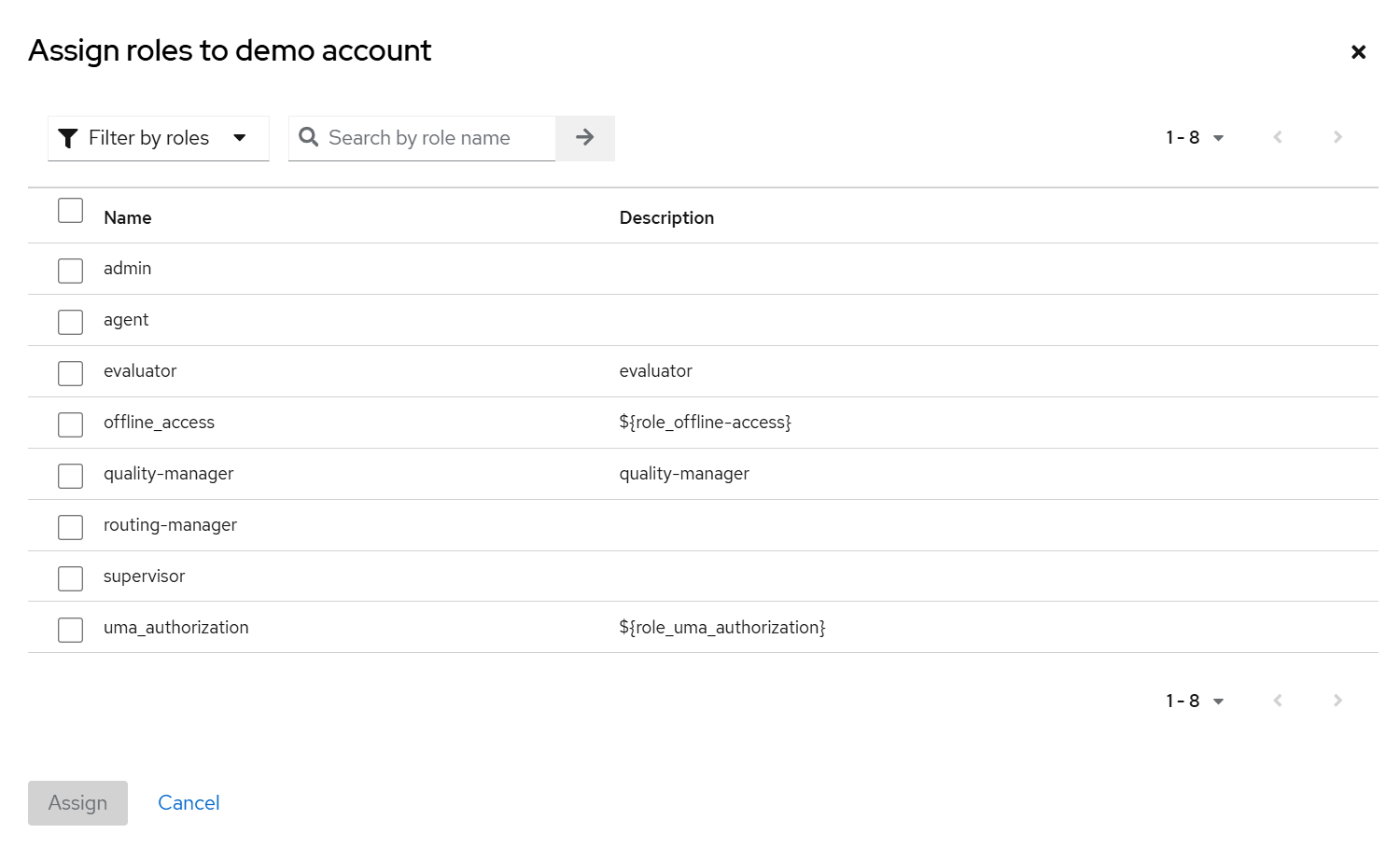
Now select the roles to want user to have. These roles will give permission to user to login and access Quality Management screens according to role like evaluator can only access Reviews List screen while Quality Manager can access Reviews List as well as Schedules and Conversation List.
Following role is compulsory:
-
agent
Other than this, you have quality-manager and evaluator role, also check which one you want user to have and click on Assign.
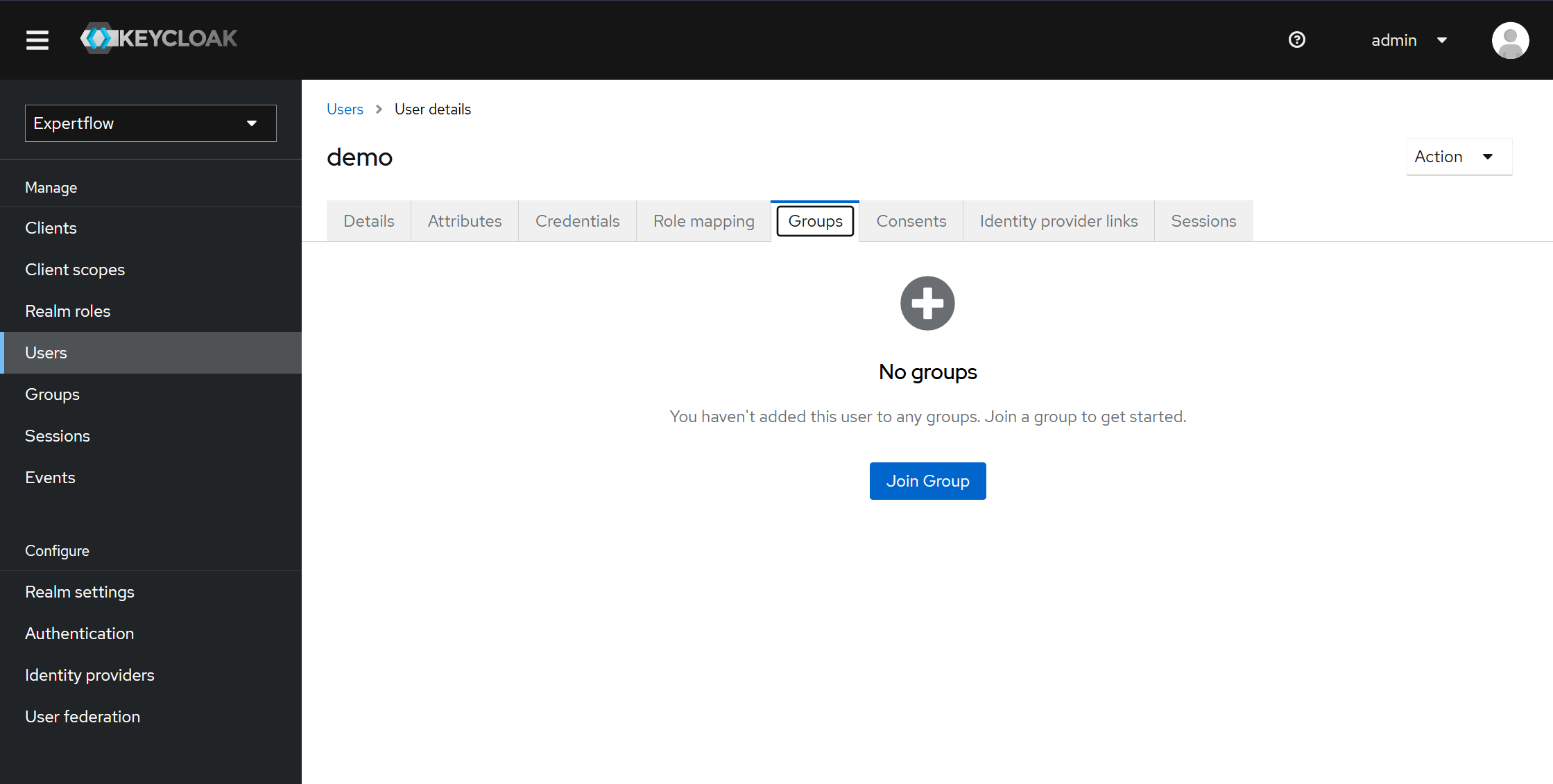
Step 4: Assigning Group to user:
Click on Groups tab. You will see following screen. Click on Join Group button in blue color.
Groups can also be assigned from Step 2 screen using Join Groups.
You will meet following screen.
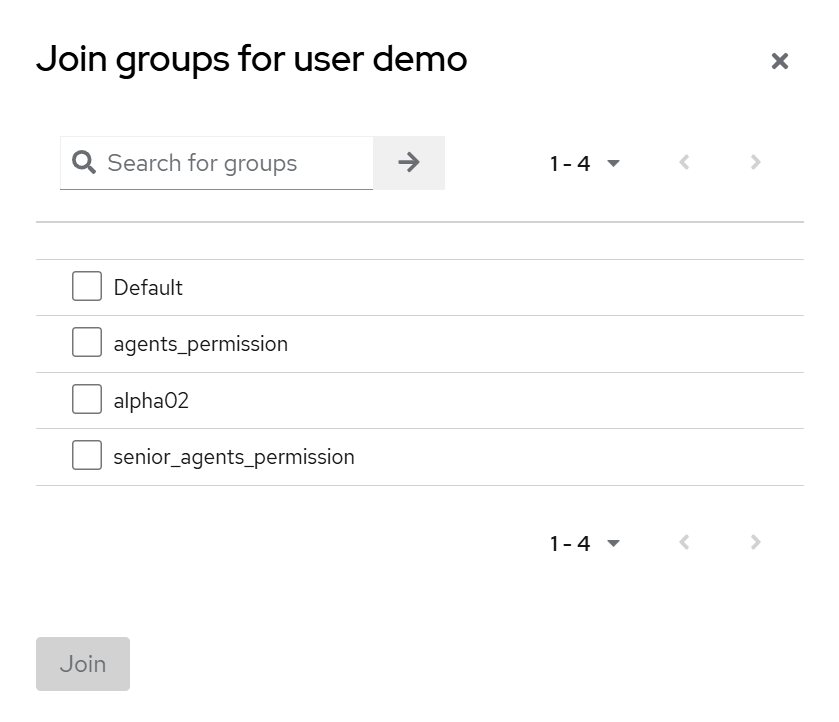
Check one of the following and click Join:
-
agents_permission
-
senior_agents_permission
You have successfully created user with required roles, group and configuration.
For logging in to Unified Admin, your user must have role of agent with group assigned and part of a team otherwise you won’t be able to login.
Follow the following section to add agent to team using admin.
Assigning team to Keycloak User:
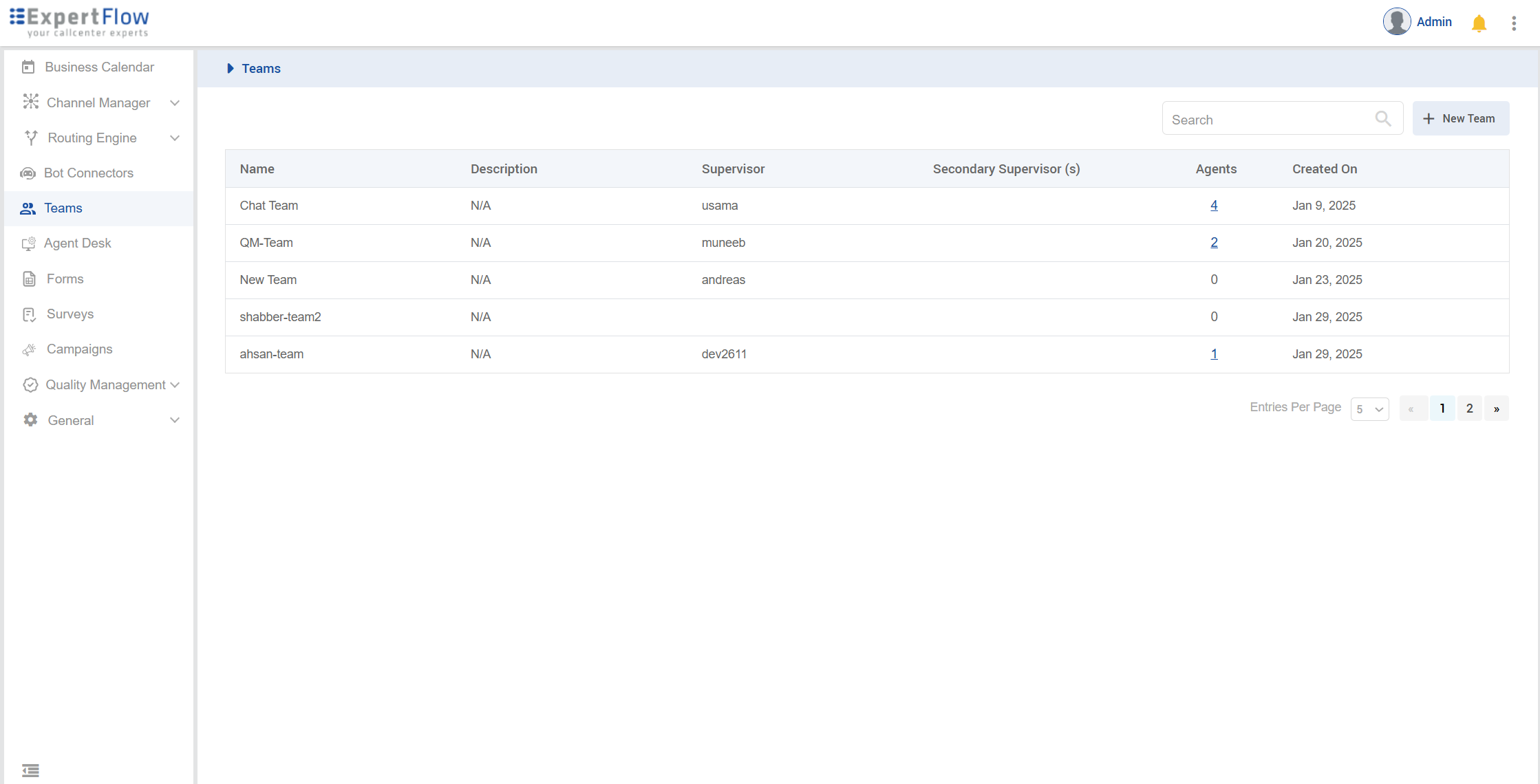
Step 1: Login to https://<FQDN>. Enter admin and admin for username and password respectively.
Click on Teams from left sidebar navigation and then click on + New Team button on left top with search box.
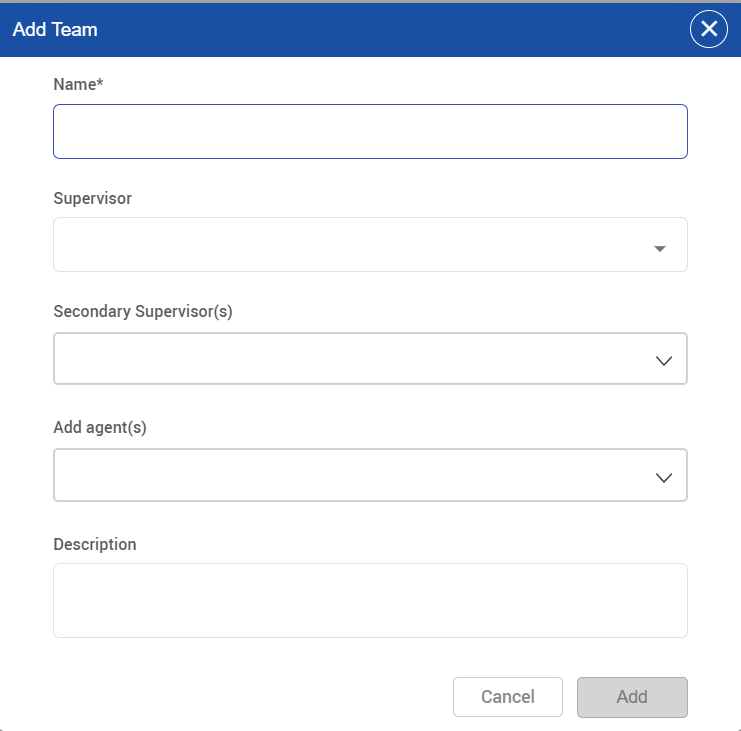
Step 2: Creating team with agent:
On clicking New Team button, a popup will appear. Fill it accordingly and click on Add. Add team name and add agent from dropdown. Your created user will be available here. Also, only user which have agent role will be available. So make sure you have assigned roles correctly.
Now user will be able to login into EFCX. Logout from top left by clicking on more button and select Logout. Try to login your user with username and password. You will be successfully able to login to EFCX.
LIMITATIONS:
-
If a wrap-up code is not found in the search, it must be added manually to retrieve the specific result.
-
Cisco wrap-up codes must exist in Unified-Admin wrap-up codes to enable schedule creation and apply conversation list filters.
-
Conference calls are not available for both inbound and outbound calls. Similarly, consult calls are also not available for outbound calls.
-
When a consulted call is transferred to the next agent, it currently does not create a conversation, leading to potential call loss. A conversation should be created to prevent this issue.
-
There are some limitations on agent-team part regarding agent deletion from keycloak. Please go through Agent Team Document limitation part for better guidance.